Thomas Hegghammer and Petter Nesser have published an alternative view to the thoughts expressed by Scott Atran in my recent post, What ISIS Plans for Europe (and Beyond). Their article, Assessing the Islamic State’s Commitment to Attacking the West, is published in the Open Access journal Perspectives on Terrorism.
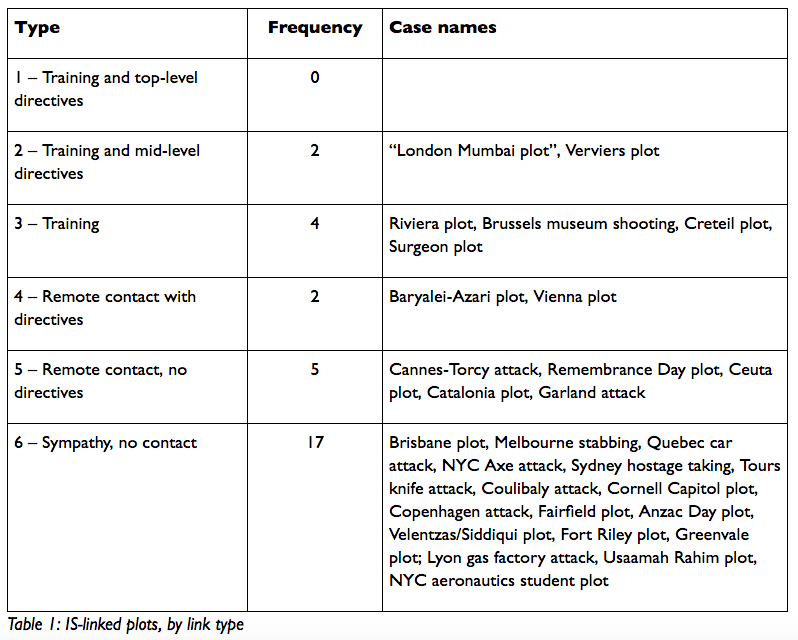
Of terrorist operations with links to a terrorist organisation like ISIS or Al Qaeda six types are identified:
- Training and top-level directives. The attacker trains in the organization’s heartland, is tasked by top leaders to attack in the West, and is supported materially by the organization in the planning and preparation process. The classic historical example is the 9/11 attack.
- Training and mid-level directives. The attacker trains in the organization’s heartland and is encouraged by mid-level cadres to carry out a more or less specified attack in the West, but has little or no interaction with the top leadership and receives little or no material support from the organization. Examples from al-Qaida’s history include the various plots by the Abu Doha network in the early 2000s or the Mohammed Merah attack in 2012.
- Training. The attacker trains in the organization’s heartland, but is not specifically instructed by anyone to attack in the West. Instead, he develops the motivation to attack in the West himself, in the belief that he is doing what the organization wants. A historical example is Mohammed Geele, who trained with al-Shabaab in Somalia, returned to Denmark, and tried to assassinate the cartoonist Kurt Westergaard in 2010.
- Remote contact with directives. The attacker communicates remotely (typically by telephone, email, or social media) and bilaterally with cadres of the organization and receives personal instructions to attack in the West. A good example from al-Qaida history is Rajib Karim, who in 2010 was instructed by Anwar al-Awlaki via encrypted email to attack airline targets in the UK.
- Remote contact without directives. The attacker communicates remotely and bilaterally with members of the organization, but does not receive instructions to attack in the West. An example would be Fort Hood shooter Nidal Malik Hassan, who exchanged emails with Anwar al-Awlaki without discussing operations.
- Sympathy, no contact. The attacker expresses ideological support for the group through his propaganda consumption, written or spoken statements, or some other aspect of his behavior, but does not communicate bilaterally with anyone in the organization. One example is Roshonara Choudhry, who stabbed a British MP in 2010, having been inspired by al-Awlaki’s online lectures.
Hegghammer and Nesser examine ISIS related attacks against the West (Europe, North America, Australia) between January 2011 and June 2015. Their tabulated findings:
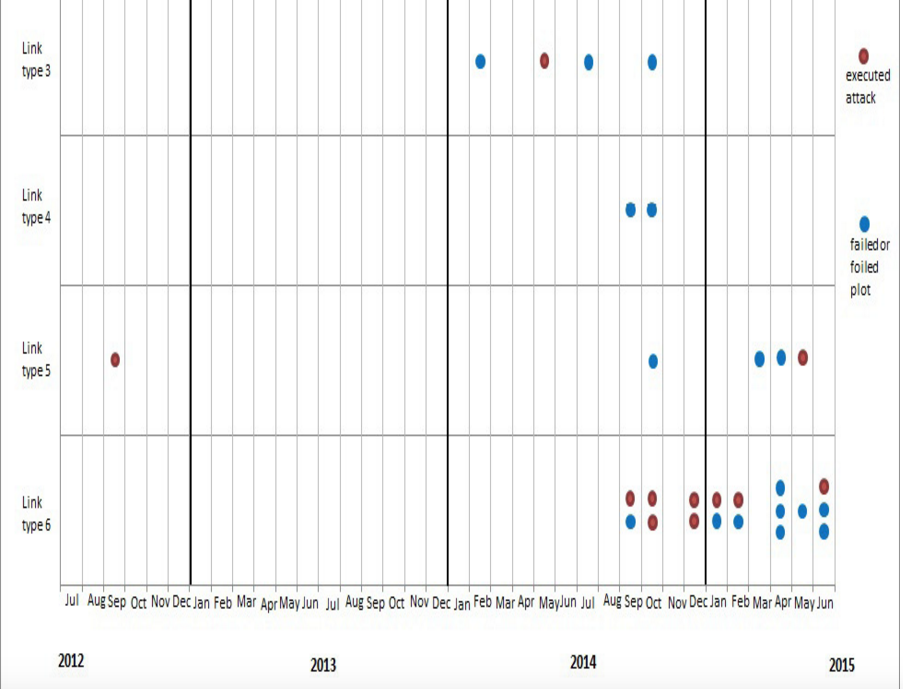
Those frequency numbers combine foiled plots as well as successful attacks. Compare the following:
So up till June 2015 there was no evidence of ISIS commitment to launch increasing numbers of attacks in the West. The threat has come, rather, from Western sympathizers who have had no contact with ISIS itself.
The title of this post can be misleading. While ISIS may not be actively planning specific attacks in the West, it is nonetheless clear that it does encourage free-lancers to act in sympathetic response to its propaganda videos, whether by joining them, donating to them, or doing whatever one can to attack “the Grey Zone”.
See the article for the detailed discussion.
If you enjoyed this post, please consider donating to Vridar. Thanks!

Why does no one do a parallel study of western attacks on the middle east. Almost all would fall in categories one and two because they are government sponsored. Except for kills of high value targets like the ISIS leader killed yesterday, we never even hear in the MSM of air and drone strikes that kill and maim far more than terrorist attacks in the west. Our terrorism, and the interests that support it (eg war profiteers and Christian zealots), are apparently not regarded as worth investigating.
I don’t think that’s fair. Bookshelves are jam-packed with analyses and histories of Western wars in the Middle East. Mountain ranges of literature have been produced about them. Many of us (probably you, too) have at some time been actively involved in attempting to do our bit to protest and help prevent such attacks by our own governments.
But I don’t believe you would at the same time consider terrorist attacks on anyone justified or not worth studying, either, would you? My hope is that more of us can actually understand what contributes to these attacks and support responses that would make a better world for us all — and that would include an end to state-sponsored terror and war, too.
Neil, yes, I agree that it is useful and important to examine the motivations and backgrounds of those who attempt to murder others, no matter who does it and where. This is especially important because some prominent anti-religious zealots have concluded, with little evidence or inquiry, that Islam is the primary cause of terrorism by Muslims. So yes, it is important to correct that lazy, bigoted assumption. But I would maintain that acknowledging the context of western aggression and imperialism, in which Muslims attacks occur, is even more important. Yes, books and articles have been written, but western responsibility is seldom part of the daily conversation on the blogs and in the media. We are in a state of willful denial. Until we acknowledge and correct our own terrorism, we will not solve the problems of terror and war for others.
Yes, I agree with your sentiments. I am not always sure of the best way to approach our collective blindness, however. My recent post listing Brussels in the context of scores of other attacks this year had that subtext. But I think our message backfires on us if we appear to minimise or excuse the horror of terrorism, too. We speak of asymmetric warfare, but both sides are doing the killing. What has happened to our collective awareness is astonishing. The power of propaganda (and self-censorship) really does appear to have been far more effective than the comparatively crude efforts of the Nazis and Stalinists.
It is important, too, to understand terrorism in all its complexity, and to understand our own terror in its complexity, too. Most people are not knowingly supporting terror and it can backfire if we appear to be accusing them of doing so without some sort of explanation as to how our system works. Look at the right-wing or conservative comments on this blog. They nearly all as good as admit their ignorance of what is really going on and they do act with an understandable (if uninformed) moral outrage.
And it’s pointless castigating the powers at the top who do know what they are doing.
I have often been thinking over how to do posts on our media and the history of propaganda in Australia — presumably there would be overlap with America, Europe, etc.